For those of you who follow my carding guides on the forum, you’ll be familiar with my emphasis on scouting before committing to any site. The flood of PMs asking for a deeper dive into the process has finally worn me down. So here we are, dissecting the art of digital scouting.
This guide is Part 1 of our deep dive into scouting. We’ll cover the basics and give you an idea of the technical approach. In the next part, we’ll dive into the technical side, showing you how to use tools like Burp Suite and Caido to really understand what you’re up against.
Most new carders can’t wait to test out their shiny new cards, eager to rack up orders as soon as they get their hands on some plastic. This is the express ticket to getting your transactions locked down and your digital fingerprint marked.
Experienced players understand that the real battle happens long before you even think about that “Pay” button. It’s about dissecting your target, understanding how they work, and finding weak spots. What security measures are you up against? Are there any vulnerabilities in their system that can be exploited? What strategies have proven effective for others?
This guide is your crash course in mastering digital intelligence. Don’t expect a step-by-step guide to “Scams for Dummies.” We develop the skills and mentality needed to analyze potential markers with surgical precision.
We go from surface-level scanning to a quick overview of technical probing. By the time we’ve completed both parts, you’ll be ready to compile a comprehensive intelligence report on any site you look at.
In this game, information is king. The more data you gather, the better your chances of a successful strike and the less likely you are to be caught with your defenses down. So get focused – it’s time to transform yourself from a clumsy amateur into a digital genius
Why Intelligence?
So why is intelligence so important? Let’s break it down. Firstly, it significantly increases your success rates. I can’t count the number of times I’ve witnessed idiots waste high-quality cards trying to brute force their way through a site, when simple intelligence would have shown that they had done extra verification that week due to increased fraud. That’s potentially thousands of dollars down the drain because someone didn’t bother to do their homework.
Intelligence also helps you avoid common pitfalls. Have you ever tried to hack a site only to find out that they use 3D Secure for every transaction? Or that they have a hard limit on purchase amounts for new accounts? That’s the kind of crap that proper intelligence uncovers.
But perhaps most importantly, good intelligence allows you to tailor your approach. Every site has its quirks, and a one-size-fits-all carding approach is a recipe for failure. Take Walmart, for example. A quick check might show that they allow address changes after purchase. Dig deeper and you’ll find that they only allow this for certain product categories. Armed with this knowledge, you can zero in on those specific categories, which will greatly increase your chances of a successful bid.
Let me drive this point home with a real life example. Last month, some cheeky asshole in one of my groups decided he was going to hit a PC parts vendor hard because he had been so lucky with them. He had a new shipment of 50 premium cards that cost around $25 a card. Without doing any recon, he turned on his anti-detect and started placing orders for high-end GPUs.
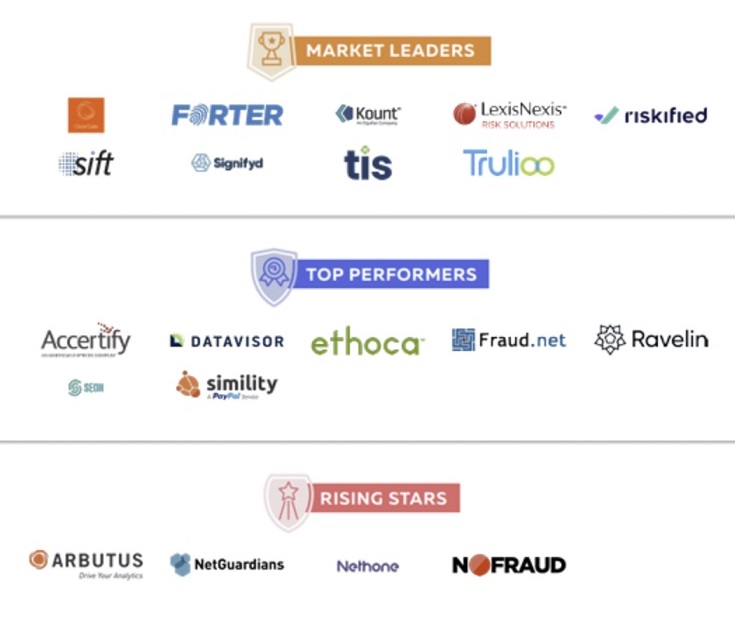
The result? 48 rejections and cancellations out of 50 attempts. It turns out the site had recently partnered with Signifyd to prevent fraud, and they were carefully screening orders for high-end electronics like a jealous girlfriend checking her man’s phone. Not only did this asshole waste over a thousand dollars worth of cards, he also burned through gigabytes of residential proxies and wasted a good 2 days of his life. All because he couldn’t be bothered to spend an hour doing proper recon.
Surface Level Checks
Okay, before we get technical, let's talk about the basics. These surface level checks are your first line of intelligence, and they can save your ass more often than you think.
Email Verification Loopholes
First, check to see if you can sign up with any email address without verification. This is pretty damn cool for a few reasons. If a site allows you to check out with any email address, you can use the cardholder's email address. Why? Because it makes their fraud system drool with glee. "Oh, look, it's the same email address we've seen a thousand times! It must be real!"
To test this, simply try signing up with a crappy email address. If it lets you proceed without sending you a verification link, you're in. This trick has saved my ass more times than I can count, especially on sites with anal fraud detection.
Changing Address After Ordering
Next, see if you can change the shipping address after purchase. This is a carder’s wet dream. You place an order with the cardholder’s address so that billing and shipping match up like a good little customer. Then, once it’s approved, you change the shipping address on your drop.
To check, Google “Change [SITE NAME] shipping address” or check Reddit. Look up other people’s experiences. If you’re feeling particularly meticulous, place a cheap order and try changing it yourself. Didn’t work? Go to customer service and ask about changing the shipping address. Their response will tell you everything you need to know.
Customer Service Response Time and Policies
Speaking of customer service, get a feel for how they work. Are they quick to respond? Do they use tickets or live chat? This information is crucial if you need to harangue them about something after ordering.
Try contacting them with a silly question and see how long it takes them to respond. Pay attention to their business hours, too. There's nothing worse than being stuck in limbo because customer service isn't available that day.
Gift Card and Digital Goods Policy
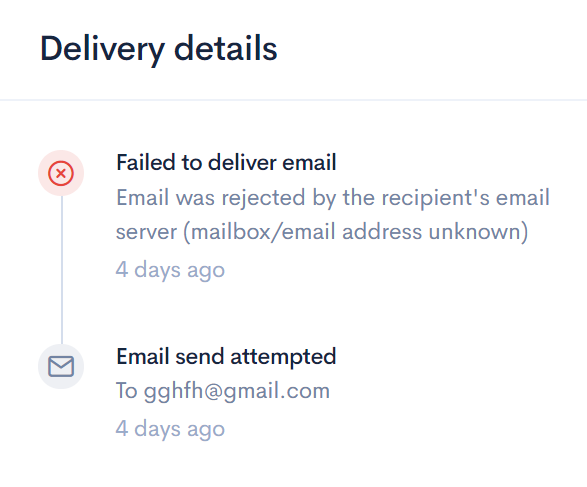
If you’re looking at gift cards or digital products, pay special attention to this. Look into their policy on changing the recipient’s email address for these orders. Why? Because just like using the cardholder’s email address for regular orders, you can use it for gift card orders too.
The trick here is to order a gift card to the cardholder’s email address, then switch it to yours once approved. Amazon is the best example of this trick, but plenty of other sites fall for it too.
Remember, these superficial checks are just an appetizer. They’re quick and easy, and can often be completed without raising any red flags. But don’t stop there. They’re just laying the groundwork for a more in-depth technical investigation, which we’ll get to next.
These checks may seem simple, but they’ve saved my ass more times than I can count. Don’t be the idiot who skips this step and wastes high-quality cards on easily avoidable crap. Take your time, do the work, and set yourself up for success before you even think about hitting checkout.
Technical Intelligence
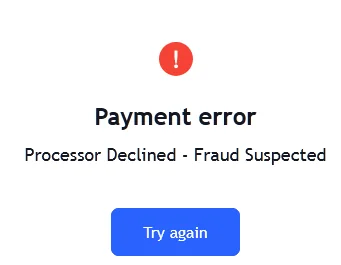
Now that we’ve covered the basics, let’s dive into the technical side of intelligence. Essentially, technical intelligence comes down to uncovering two important pieces of information: the payment processor and the fraud protection system the site implements.
Why is this important? Because knowing this allows us to fine-tune our approach with surgical precision. Let’s say the site uses Stripe. If your cards have been run through other Stripe-powered stores (like Shopify), you might want to save those cards for this swipe. Why? Because Stripes has the memory of an elephant and will quickly flag those cards.
Different fraud protection systems have different quirks, too. Forter, for example, looks at your transaction history. Signifyd, on the other hand, treats email addresses like they’re the Holy Grail. Knowing these quirks can make or break your operation.
So how do we uncover this goldmine of information? There are three main tools in our toolbox: Caido, Burp Suite, and good old Chrome Developer Tools (specifically the Network tab).
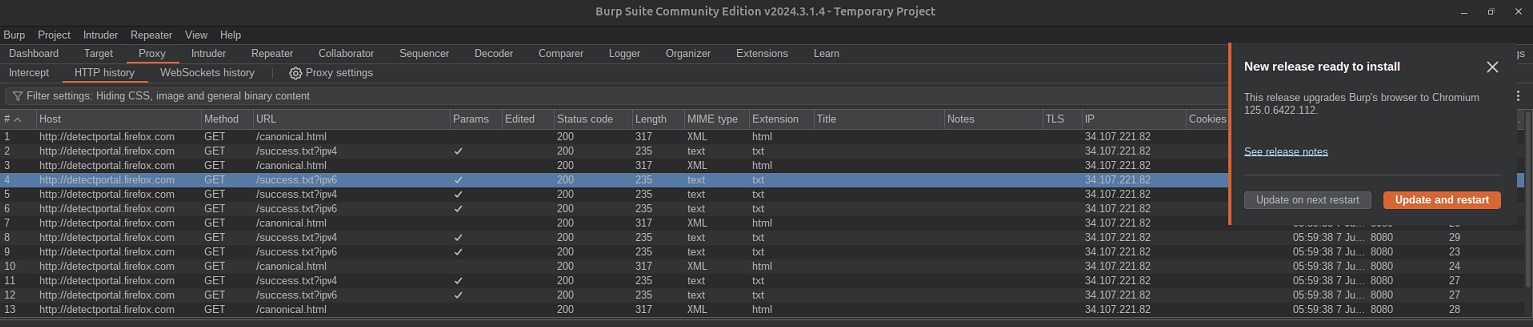
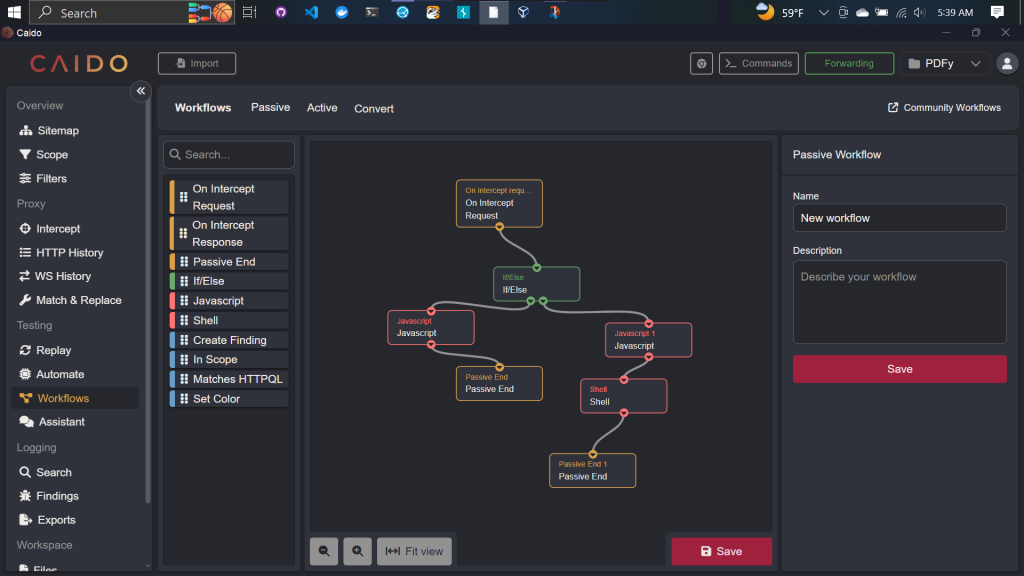
These tools let us look under the hood of a website, showing us the requests and responses flying back and forth between our browser and their system. It’s like X-ray vision for websites. We can see what JavaScript they’re injecting into our session, what data they’re sending them (like our fingerprints or even our damn mouse movements), and more.
Caido and Burp Suite are the big guns here. They’re full-featured interception proxies that give you god-like control over HTTP/S traffic. Chrome’s developer tools, while not as powerful, are built right into your browser and can still uncover a ton of useful crap.
Now, I know some of you are probably salivating at the thought of diving deeper into this technical stuff. But hold your horses. Explaining all the intricacies of these tools and how to interpret the data they throw out? That’s a whole other matter. We’d be here all day, and I have better things to do than write a novel.
Here’s the deal: We’re going to cover all that juicy tech shit in Part 2 of this guide. We’ll go over each tool, show you how to use them, and most importantly, how to interpret what you find. We’ll break down real-world examples, showing you exactly what to look for when you’re doing your own reconnaissance.
For now, just understand that these tools exist and what they can do for you. They’re the difference between flying blind and having a site protection plan.
Secondary Sources
While technical reconnaissance gives you the facts, secondary sources fill in the gaps with real information. This is where you become a digital detective, piecing together an internet puzzle.
Practice your Google fu first. Don’t just search for the company name, dig deeper. Look for annual reports, press releases, and tech blogs. These can reveal all sorts of useful information about their payment systems, security updates, or even data breaches. Is the company bragging about its new AI-powered fraud detection? This is your signal to be careful.
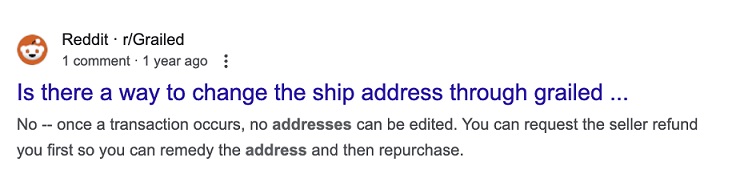
Reddit and forums are gold. Search for the site name and keywords like order problem, “scam,” or “account locked.” You’ll find plenty of angry customers describing their experiences. Look for patterns. If multiple users report their accounts being locked after changing their shipping address, you know how to avoid this trick.
Don’t overlook smaller forums, either. Sometimes the best information comes from unexpected places. I once found a major weakness in a major electronics retailer’s system hidden in a thread on a PC building forum.
Social media is your window into customer service practices. Monitor the company’s Twitter and FB. See how they respond to complaints. Are they quick to offer refunds? Do they have a dedicated fraud team? This information can be helpful in planning your strategy.
Check their job listings, too. A company hiring for fraud prevention positions may be tightening their measures. A company that fires its loss prevention team can be an easy target.
Remember, the goal here is not just to gather information, but to get a complete picture of your target. How do they resolve disputes? What are the scam alerts they receive? What loopholes have others successfully exploited?
Don’t just look at the latest posts. Sometimes old information is just as valuable. A company’s fraud prevention may have changed, but the core policies remain the same.
All of this takes time and patience. But trust me when I say it’s worth it. I’ve seen carders pull off six-figure scams because they found one small detail in a year-old Reddit comment.
It’s not just about not getting caught, it’s about crafting the perfect approach. The more you know about your target, the more you can fine-tune your approach. You may find that they’re lenient with new customers, or never review orders below a certain amount. This is the kind of intelligence that turns a risky attack into a smooth operation.
So before you even think about placing an order, do your homework. Scour every corner of the internet. Create a profile of your target that would make the CIA jealous. Because in this game, information isn’t just power, it’s profit.
Putting it all together
Okay, let’s come full circle. We’ve covered the basics of intelligence, from surface-level checks to a little technical probing and secondary-source searching. But knowing these things is only half the story. The real skill is integrating all this intelligence into a strategy.
Before you even think about placing an order, gather everything you’ve learned about your target. Create a preliminary checklist specifically for the location you’re going to attack. This isn’t just a box-ticking exercise — it’s your battle plan.
Your checklist should cover:
Remember, scouting isn’t a one-time thing. The carding landscape is constantly changing. What worked yesterday could get you flagged today. Stay alert, stay on top of your intel, and never stop learning.
In Part 2, we’ll dive deeper into the technical side of scouting. In the meantime, start practicing these techniques. Develop your skills, hone your instincts, and approach every potential shot like a pro.
Because in this game, the difference between success and failure often comes down to the work you do before you hit that checkout button.
Now go ahead and start acting like your money depends on it — because it does.
This guide is Part 1 of our deep dive into scouting. We’ll cover the basics and give you an idea of the technical approach. In the next part, we’ll dive into the technical side, showing you how to use tools like Burp Suite and Caido to really understand what you’re up against.
Most new carders can’t wait to test out their shiny new cards, eager to rack up orders as soon as they get their hands on some plastic. This is the express ticket to getting your transactions locked down and your digital fingerprint marked.
Experienced players understand that the real battle happens long before you even think about that “Pay” button. It’s about dissecting your target, understanding how they work, and finding weak spots. What security measures are you up against? Are there any vulnerabilities in their system that can be exploited? What strategies have proven effective for others?
This guide is your crash course in mastering digital intelligence. Don’t expect a step-by-step guide to “Scams for Dummies.” We develop the skills and mentality needed to analyze potential markers with surgical precision.
We go from surface-level scanning to a quick overview of technical probing. By the time we’ve completed both parts, you’ll be ready to compile a comprehensive intelligence report on any site you look at.
In this game, information is king. The more data you gather, the better your chances of a successful strike and the less likely you are to be caught with your defenses down. So get focused – it’s time to transform yourself from a clumsy amateur into a digital genius
Why Intelligence?
So why is intelligence so important? Let’s break it down. Firstly, it significantly increases your success rates. I can’t count the number of times I’ve witnessed idiots waste high-quality cards trying to brute force their way through a site, when simple intelligence would have shown that they had done extra verification that week due to increased fraud. That’s potentially thousands of dollars down the drain because someone didn’t bother to do their homework.
Intelligence also helps you avoid common pitfalls. Have you ever tried to hack a site only to find out that they use 3D Secure for every transaction? Or that they have a hard limit on purchase amounts for new accounts? That’s the kind of crap that proper intelligence uncovers.
But perhaps most importantly, good intelligence allows you to tailor your approach. Every site has its quirks, and a one-size-fits-all carding approach is a recipe for failure. Take Walmart, for example. A quick check might show that they allow address changes after purchase. Dig deeper and you’ll find that they only allow this for certain product categories. Armed with this knowledge, you can zero in on those specific categories, which will greatly increase your chances of a successful bid.
Let me drive this point home with a real life example. Last month, some cheeky asshole in one of my groups decided he was going to hit a PC parts vendor hard because he had been so lucky with them. He had a new shipment of 50 premium cards that cost around $25 a card. Without doing any recon, he turned on his anti-detect and started placing orders for high-end GPUs.
The result? 48 rejections and cancellations out of 50 attempts. It turns out the site had recently partnered with Signifyd to prevent fraud, and they were carefully screening orders for high-end electronics like a jealous girlfriend checking her man’s phone. Not only did this asshole waste over a thousand dollars worth of cards, he also burned through gigabytes of residential proxies and wasted a good 2 days of his life. All because he couldn’t be bothered to spend an hour doing proper recon.
Surface Level Checks
Okay, before we get technical, let's talk about the basics. These surface level checks are your first line of intelligence, and they can save your ass more often than you think.
Email Verification Loopholes
First, check to see if you can sign up with any email address without verification. This is pretty damn cool for a few reasons. If a site allows you to check out with any email address, you can use the cardholder's email address. Why? Because it makes their fraud system drool with glee. "Oh, look, it's the same email address we've seen a thousand times! It must be real!"
To test this, simply try signing up with a crappy email address. If it lets you proceed without sending you a verification link, you're in. This trick has saved my ass more times than I can count, especially on sites with anal fraud detection.
Changing Address After Ordering
Next, see if you can change the shipping address after purchase. This is a carder’s wet dream. You place an order with the cardholder’s address so that billing and shipping match up like a good little customer. Then, once it’s approved, you change the shipping address on your drop.
To check, Google “Change [SITE NAME] shipping address” or check Reddit. Look up other people’s experiences. If you’re feeling particularly meticulous, place a cheap order and try changing it yourself. Didn’t work? Go to customer service and ask about changing the shipping address. Their response will tell you everything you need to know.
Customer Service Response Time and Policies
Speaking of customer service, get a feel for how they work. Are they quick to respond? Do they use tickets or live chat? This information is crucial if you need to harangue them about something after ordering.
Try contacting them with a silly question and see how long it takes them to respond. Pay attention to their business hours, too. There's nothing worse than being stuck in limbo because customer service isn't available that day.
Gift Card and Digital Goods Policy
If you’re looking at gift cards or digital products, pay special attention to this. Look into their policy on changing the recipient’s email address for these orders. Why? Because just like using the cardholder’s email address for regular orders, you can use it for gift card orders too.
The trick here is to order a gift card to the cardholder’s email address, then switch it to yours once approved. Amazon is the best example of this trick, but plenty of other sites fall for it too.
Remember, these superficial checks are just an appetizer. They’re quick and easy, and can often be completed without raising any red flags. But don’t stop there. They’re just laying the groundwork for a more in-depth technical investigation, which we’ll get to next.
These checks may seem simple, but they’ve saved my ass more times than I can count. Don’t be the idiot who skips this step and wastes high-quality cards on easily avoidable crap. Take your time, do the work, and set yourself up for success before you even think about hitting checkout.
Technical Intelligence
Now that we’ve covered the basics, let’s dive into the technical side of intelligence. Essentially, technical intelligence comes down to uncovering two important pieces of information: the payment processor and the fraud protection system the site implements.
Why is this important? Because knowing this allows us to fine-tune our approach with surgical precision. Let’s say the site uses Stripe. If your cards have been run through other Stripe-powered stores (like Shopify), you might want to save those cards for this swipe. Why? Because Stripes has the memory of an elephant and will quickly flag those cards.
Different fraud protection systems have different quirks, too. Forter, for example, looks at your transaction history. Signifyd, on the other hand, treats email addresses like they’re the Holy Grail. Knowing these quirks can make or break your operation.
So how do we uncover this goldmine of information? There are three main tools in our toolbox: Caido, Burp Suite, and good old Chrome Developer Tools (specifically the Network tab).
These tools let us look under the hood of a website, showing us the requests and responses flying back and forth between our browser and their system. It’s like X-ray vision for websites. We can see what JavaScript they’re injecting into our session, what data they’re sending them (like our fingerprints or even our damn mouse movements), and more.
Caido and Burp Suite are the big guns here. They’re full-featured interception proxies that give you god-like control over HTTP/S traffic. Chrome’s developer tools, while not as powerful, are built right into your browser and can still uncover a ton of useful crap.
Now, I know some of you are probably salivating at the thought of diving deeper into this technical stuff. But hold your horses. Explaining all the intricacies of these tools and how to interpret the data they throw out? That’s a whole other matter. We’d be here all day, and I have better things to do than write a novel.
Here’s the deal: We’re going to cover all that juicy tech shit in Part 2 of this guide. We’ll go over each tool, show you how to use them, and most importantly, how to interpret what you find. We’ll break down real-world examples, showing you exactly what to look for when you’re doing your own reconnaissance.
For now, just understand that these tools exist and what they can do for you. They’re the difference between flying blind and having a site protection plan.
Secondary Sources
While technical reconnaissance gives you the facts, secondary sources fill in the gaps with real information. This is where you become a digital detective, piecing together an internet puzzle.
Practice your Google fu first. Don’t just search for the company name, dig deeper. Look for annual reports, press releases, and tech blogs. These can reveal all sorts of useful information about their payment systems, security updates, or even data breaches. Is the company bragging about its new AI-powered fraud detection? This is your signal to be careful.
Reddit and forums are gold. Search for the site name and keywords like order problem, “scam,” or “account locked.” You’ll find plenty of angry customers describing their experiences. Look for patterns. If multiple users report their accounts being locked after changing their shipping address, you know how to avoid this trick.
Don’t overlook smaller forums, either. Sometimes the best information comes from unexpected places. I once found a major weakness in a major electronics retailer’s system hidden in a thread on a PC building forum.
Social media is your window into customer service practices. Monitor the company’s Twitter and FB. See how they respond to complaints. Are they quick to offer refunds? Do they have a dedicated fraud team? This information can be helpful in planning your strategy.
Check their job listings, too. A company hiring for fraud prevention positions may be tightening their measures. A company that fires its loss prevention team can be an easy target.
Remember, the goal here is not just to gather information, but to get a complete picture of your target. How do they resolve disputes? What are the scam alerts they receive? What loopholes have others successfully exploited?
Don’t just look at the latest posts. Sometimes old information is just as valuable. A company’s fraud prevention may have changed, but the core policies remain the same.
All of this takes time and patience. But trust me when I say it’s worth it. I’ve seen carders pull off six-figure scams because they found one small detail in a year-old Reddit comment.
It’s not just about not getting caught, it’s about crafting the perfect approach. The more you know about your target, the more you can fine-tune your approach. You may find that they’re lenient with new customers, or never review orders below a certain amount. This is the kind of intelligence that turns a risky attack into a smooth operation.
So before you even think about placing an order, do your homework. Scour every corner of the internet. Create a profile of your target that would make the CIA jealous. Because in this game, information isn’t just power, it’s profit.
Putting it all together
Okay, let’s come full circle. We’ve covered the basics of intelligence, from surface-level checks to a little technical probing and secondary-source searching. But knowing these things is only half the story. The real skill is integrating all this intelligence into a strategy.
Before you even think about placing an order, gather everything you’ve learned about your target. Create a preliminary checklist specifically for the location you’re going to attack. This isn’t just a box-ticking exercise — it’s your battle plan.
Your checklist should cover:
- Email Verification Loopholes
- Change of Address Policy
- Customer support response time
- Payment processor and anti-fraud system
- Known factors that contribute to fraud detection
- Successful Strategies Others Have Used
Remember, scouting isn’t a one-time thing. The carding landscape is constantly changing. What worked yesterday could get you flagged today. Stay alert, stay on top of your intel, and never stop learning.
In Part 2, we’ll dive deeper into the technical side of scouting. In the meantime, start practicing these techniques. Develop your skills, hone your instincts, and approach every potential shot like a pro.
Because in this game, the difference between success and failure often comes down to the work you do before you hit that checkout button.
Now go ahead and start acting like your money depends on it — because it does.
Last edited:


