You’ve probably heard me rant about Telegram’s bullshit in the Protecting Your Telegram thread. Yes, it’s the darling of the scam world — slick interface, easy to use, everyone uses it. And for everyday stuff, it gets the job done. Even Signal has its place — it’s a decent choice for normals who want a little more privacy. But let’s not be ridiculous: If you’re moving serious weight or running complex transactions, Telegram and Signal are playing with fire. They’re cosying up to governments by handing over data.
So, what’s the alternative? That’s where SimpleX comes in. This isn’t your average messaging app. It’s a secure communications platform built from the ground up for people who can’t afford to have their shit tracked, tracked, or handed over to the feds.
Why Your Favorite Messenger Might Not Be Enough

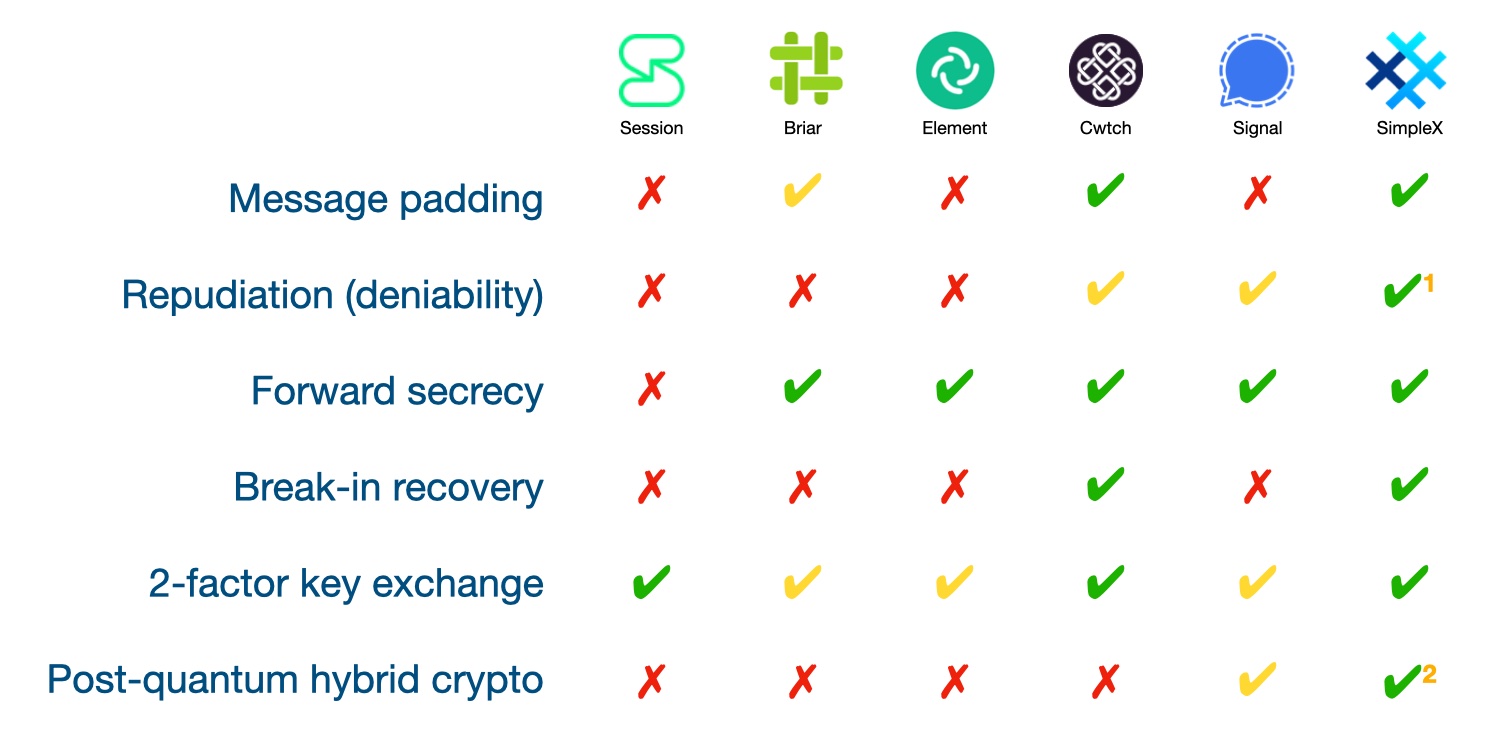
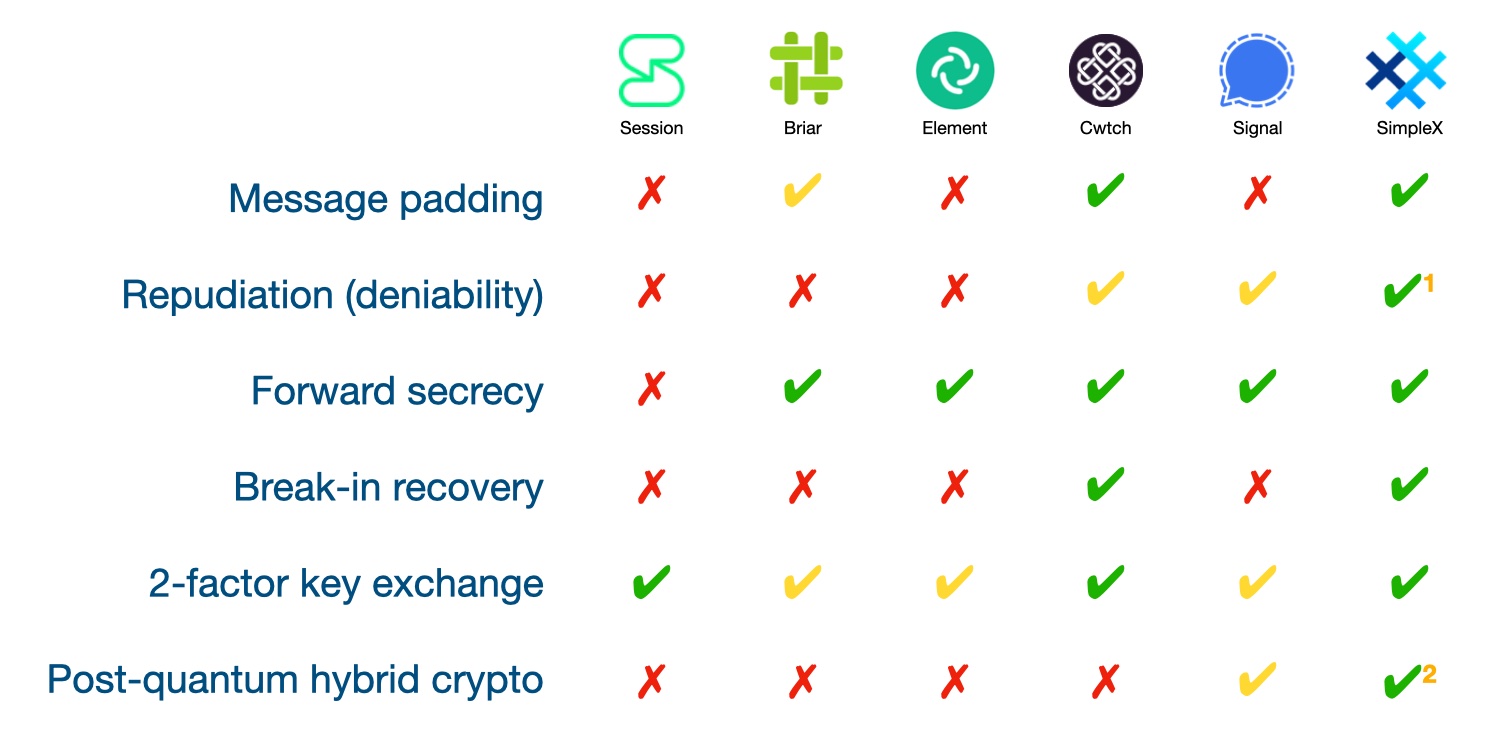
Let's get this straight: Most of the popular messaging apps have their benefits, but they also have their drawbacks.
These platforms are great for everyday communication, but for our work, you need to consider the risks. Every message you send, every contact you add, all of it is potentially traceable.
Think about it: every time you use these apps, you leave a digital footprint. It may be weak, but it’s there.
SimpleX

SimpleX is different. It’s not some clunky attempt to bolt security onto an existing platform. It’s privacy by design, from the ground up.
Here’s the deal: SimpleX doesn’t use any identifiers. No phone numbers, no usernames, nothing. It’s like slipping into a crowded room wearing a mask—no one knows who you are or who you’re talking to.
How It Works
Forget everything you thought you knew about how messaging apps work. SimpleX throws that whole framework out the window. Instead of relying on central servers that act as nosy switchboard operators, SimpleX creates a unique, ever-changing network of paths for every conversation.

Imagine sending a message through a maze. Every time you send something, the walls shift, the paths change, and new routes are created. Even the people running the maze have no idea who is sending what to whom.
This project means:
It's like having a network of secret tunnels. No one can track you because the paths you use today may not exist tomorrow.
Why SimpleX is a godsend for our work
Absolute anonymity
There is literally nothing tying you to your messages. No phone number, no email, no permanent identifier. You are a digital ghost. This is important when you need to work completely offline.
Military-grade encryption
Everything is encrypted by default – messages, files, even metadata. SimpleX uses seriously hardcore cryptography (NaCl with Curve25519). You don’t have to be a cryptographer to use it, just know that it’s virtually uncrackable.
Complete Control
You’re in the driver’s seat. You choose which servers to use, how long messages are stored, and when they’re deleted. You can even run your own server if you’re paranoid (and you should be).
Protect Metadata
Most messaging apps leak metadata. It’s the who, when, and where of your conversations, and it can be as incriminating as the messages themselves. SimpleX eliminates this risk by using separate time paths for each conversation.
Testing SimpleX
Look, anyone can claim their app is secure. But SimpleX backed up their words with action and hired Trail of Bits – one of the most respected names in security auditing – to take apart their code.

The result? They found a few minor issues that have already been fixed. That's a big deal. It means security isn't just marketing hype, it's real. When you have top-level security experts giving their seal of approval, you know you're dealing with something legitimate.
The audit covered everything from encryption algorithms to the way messages are routed.
Getting Started with SimpleX

Professional tips for maximum safety
Bottom Line
If you’re still fiddling with popular messaging apps for your most sensitive operations, you’re betting big. Telegram and Signal have their uses, but they’re not built for this level of OPSEC.
SimpleX is the way to go. It’s not the most popular app, and that’s exactly why it’s perfect for us. No corporate ties, no government backdoors, and no way for your messages to be traced back to you.
While other apps are busy patching holes, SimpleX was built from the ground up to be a fortress of privacy.
Remember: in this game, security is not a luxury, it’s a necessity. One mistake with the wrong messenger can cost you everything. Don’t take chances.
Switch to SimpleX. Your freedom may depend on it.
(c) Telegram: d0ctrine
So, what’s the alternative? That’s where SimpleX comes in. This isn’t your average messaging app. It’s a secure communications platform built from the ground up for people who can’t afford to have their shit tracked, tracked, or handed over to the feds.
Why Your Favorite Messenger Might Not Be Enough
Let's get this straight: Most of the popular messaging apps have their benefits, but they also have their drawbacks.
- Telegram: It's popular for a reason - it's fast and convenient. But lately they've become too willing to cooperate with the authorities. Good for informal conversations, but a potential risk for serious business.
- Signal: A step up in privacy, sure. But this reliance on phone numbers is a weak link. Encryption is great, but what's the point if your number can be tracked?
- WhatsApp: Facebook's Playground. Convenient, but Do You Trust Them With Your Data?
- Matrix: Decentralization sounds good on paper, but it has security flaws. Plus, your metadata is still there.
These platforms are great for everyday communication, but for our work, you need to consider the risks. Every message you send, every contact you add, all of it is potentially traceable.
Think about it: every time you use these apps, you leave a digital footprint. It may be weak, but it’s there.
SimpleX
SimpleX is different. It’s not some clunky attempt to bolt security onto an existing platform. It’s privacy by design, from the ground up.
Here’s the deal: SimpleX doesn’t use any identifiers. No phone numbers, no usernames, nothing. It’s like slipping into a crowded room wearing a mask—no one knows who you are or who you’re talking to.
How It Works
Forget everything you thought you knew about how messaging apps work. SimpleX throws that whole framework out the window. Instead of relying on central servers that act as nosy switchboard operators, SimpleX creates a unique, ever-changing network of paths for every conversation.
Imagine sending a message through a maze. Every time you send something, the walls shift, the paths change, and new routes are created. Even the people running the maze have no idea who is sending what to whom.
- Encryption: Your message is encrypted on your device before it leaves. Only the person you send it to has the key to unlock it.
- Queue-based delivery: Your message is sent to a secure digital mailbox (queue) that only your recipient can verify. The mailbox itself doesn't know who owns it or what's inside - it simply stores encrypted messages until they're picked up.
- Unique receiving addresses: Each conversation gets its own set of one-way mailboxes. There is no address book or directory of users - just randomly generated receiving addresses that cannot be traced back to anyone.
- Identity-free design: You don't need usernames or accounts. Instead, when you connect to someone, you exchange special "connection addresses" that only work for that conversation. Even if someone intercepts these addresses, they can't use them to find out who's talking to whom.
- One-way streets: Messages only go one way through each mailbox. When your friend wants to reply, they use a completely different mailbox. This means there is no way to trace messages back to their source.
This project means:
- There are no usernames or accounts to track.
- No saved contact lists
- There is no way to see who is talking to whom.
- There is no central point that knows anything about users or their connections.
- Even the servers can't read your messages or know who they belong to.
It's like having a network of secret tunnels. No one can track you because the paths you use today may not exist tomorrow.
Why SimpleX is a godsend for our work
Absolute anonymity
There is literally nothing tying you to your messages. No phone number, no email, no permanent identifier. You are a digital ghost. This is important when you need to work completely offline.
Military-grade encryption
Everything is encrypted by default – messages, files, even metadata. SimpleX uses seriously hardcore cryptography (NaCl with Curve25519). You don’t have to be a cryptographer to use it, just know that it’s virtually uncrackable.
Complete Control
You’re in the driver’s seat. You choose which servers to use, how long messages are stored, and when they’re deleted. You can even run your own server if you’re paranoid (and you should be).
Protect Metadata
Most messaging apps leak metadata. It’s the who, when, and where of your conversations, and it can be as incriminating as the messages themselves. SimpleX eliminates this risk by using separate time paths for each conversation.
Testing SimpleX
Look, anyone can claim their app is secure. But SimpleX backed up their words with action and hired Trail of Bits – one of the most respected names in security auditing – to take apart their code.

The result? They found a few minor issues that have already been fixed. That's a big deal. It means security isn't just marketing hype, it's real. When you have top-level security experts giving their seal of approval, you know you're dealing with something legitimate.
The audit covered everything from encryption algorithms to the way messages are routed.
Getting Started with SimpleX

- Download: Download SimpleX Chat from your app store.
- No registration: just open the app and start using it. No registration.
- Local Database Encryption: Go to settings and enable local database encryption. This is important - don't miss it.
- Enable Tor: For added security, use Tor. SimpleX has built-in support, so it's easy to set up.
Professional tips for maximum safety
- Strong Passphrase: Use a long, complex passphrase for your local database. Don't use something silly like "password123".
- Auto-delete messages: Set messages to self-destruct after a certain amount of time. The less data you store, the less you can lose.
- Dedicated Device: If you're really serious, use SimpleX on a separate device that's separate from your personal life.
- Stay up to date: Keep the app updated. Updates often include important security fixes.
- Separation: Never use the same SimpleX profile for different operations. Treat each one as a separate entity.
Bottom Line
If you’re still fiddling with popular messaging apps for your most sensitive operations, you’re betting big. Telegram and Signal have their uses, but they’re not built for this level of OPSEC.
SimpleX is the way to go. It’s not the most popular app, and that’s exactly why it’s perfect for us. No corporate ties, no government backdoors, and no way for your messages to be traced back to you.
While other apps are busy patching holes, SimpleX was built from the ground up to be a fortress of privacy.
Remember: in this game, security is not a luxury, it’s a necessity. One mistake with the wrong messenger can cost you everything. Don’t take chances.
Switch to SimpleX. Your freedom may depend on it.
(c) Telegram: d0ctrine
