The digital advertising space is a money printer for those who know how to use it properly. When you run ads with cards, you’re essentially converting cards into legitimate traffic, conversions, and money.
While TikTok and Facebook have recently started tightening up their fancy AI-powered verification systems, Snapchat is still running with its outdated, non-AI verification processes. It’s like they missed the security memo everyone else got. Their prehistoric verification system is great for carders who have been pushed out of other platforms due to advanced fraud detection.
Snapchat Ads
While the major platforms have tightened up their ad platforms, Snapchat is in that perfect middle ground — popular enough to drive serious traffic, but with security holes you can exploit without breaking a sweat. Their user base is largely made up of teens and young adults with disposable income and zero impulse control. These kids will click on anything shiny that will stop their friends from taking selfies with a dog filter.

What else makes Snap’s ad platform so great is its simplicity. The targeting works well enough to zero in on a specific teen demographic — sneakerheads, aspiring influencers, makeup-obsessed people — allowing you to promote products these kids desperately want. Dropshipping fake streetwear? Questionable supplements? Fake designer crap? Card-sniffing scam pages? Snapchat’s teen market will eat it up. They don’t vet your ads like Facebook’s digital Gestapo, and if you know what you’re doing, their payment system has weaknesses you can exploit all day long.

Antifraud and cloaking
You need to understand that Snapchat’s core security revolves around checking your landing pages. Their scanners scan your landing URLs for fraudulent schemes, malware, or content they’ve previously banned. Once they flag your domain, it’s dead — they blacklist it before you can use your card credits.
Using clean cards isn’t that important, what matters is that you rotate domains. Their main payment processor is dumb as a rock: no anti-fraud, no 3DS, nothing. When your card is declined or Snap bans an account, they don’t just kill your profile — they destroy your entire domain. That URL is gone forever. You need to keep a stack of fresh or old domains ready, all pointing to your main server.

For added protection, set up server-side cloaking, which shows Snap's crawlers a legitimate page while sending real users to your cash-rich site. The crawler uses predictable IP ranges and user-agent strings - filter these out and send them a clean, compliant landing page while real visitors see the shady crap you're actually advertising. This part is a bit of a complex topic, and I covered parts of it in the "Cloaking and carding of advertisements" thread.
Remember: one domain = one account. If any part fails, delete everything and start over. In practice, this means you can set up one server, map multiple domains to it, and continue showing ads with new combinations. This server becomes your base of operations while you cycle through domains and maps, maximizing your efficiency without having to rebuild your entire infrastructure each time.
 WARNING
WARNING 
One of the ways anti-fraud systems detect and reject your transactions is by checking whether the card has been used elsewhere. This means that cards that are resold at multiple stores and frequently re-checked for validity will be rejected outright.
Luckily, BinX has a free tool that will help you assess whether the card you are about to buy is being resold at multiple stores. And the best part is that it’s all FREE:
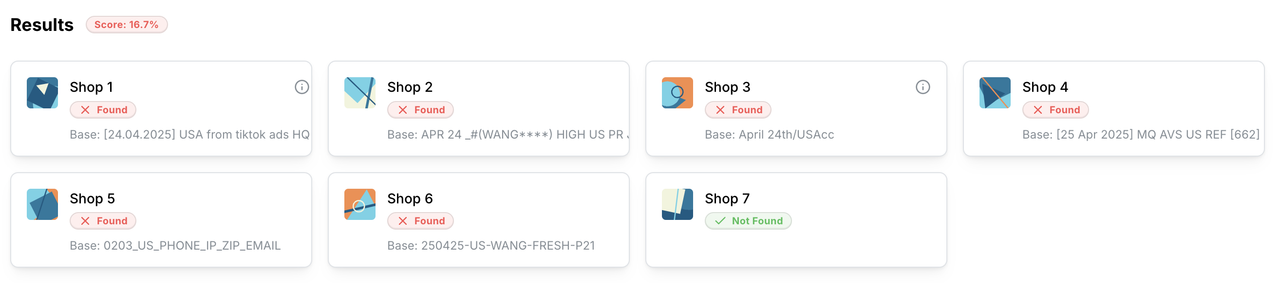
Now you’ll know if a card is bad before you buy it.
Check it out here: https://binx.cc/tools/resell
Prepay Ad Balance
Another great thing about Snapchat advertising is how easy it is to use the prepay option. Prepay Ad Balance is arguably the best tool for carders on any ad platform — it forces Snapchat to let you top up your balance up front, instead of their standard recurring billing.
Why is this important? With standard billing, Snapchat (or other platforms) charge your card certain amounts as ads run. Every charge is another damn roll of the dice — will the card work or has it already been reported? One rejection and your entire operation will collapse. But with prepay, you’ll empty the entire card in one fell swoop before any chargebacks occur. Essentially, you’re preloading all the funds on that card before it’s destroyed.

Load up a new card with $500–$1,000, burn through that balance with aggressive campaigns, and by the time the cardholder notices and reports it, you’ve already converted it into traffic. No more sweating every time Snap’s payment system decides to charge your card.
Unlike Facebook or TikTok, where pre-pay is a standard option, Snapchat hides this feature. It only appears under certain conditions that I haven’t fully mapped out yet. One reliable trigger seems to be using high-income zip codes when initially setting up a business account — try 90210 (Beverly Hills), 76092 (Southlake, TX), or other wealthy areas.
Don’t worry about using fancy zip codes during signup — the business address you enter has absolutely nothing to do with your card’s payment details. You can still add any card with any billing address to your account later. The high-income zip code is only needed for Snapchat’s system to offer the prepaid option.
When the prepaid option appears, add your card and pounce on it. This is your ticket to getting the most out of each card before it burns out.
Requirements and Process
With all that said, here’s the process:
Setting up your account:
Payment method:
Domain Management:
Campaign structure:

Remember: if any part of your transaction is flagged, throw it ALL away and start over. Don't get sentimental about accounts or domains - they are disposable tools, not pets. Also, if you overdo it by doing 5,000-10,000 on new accounts, Snap (like FB) may ask for a mini-spend code, although I have not encountered this at all.

Conclusion
Snapchat remains one of the last semi-vulnerable major ad platforms for carding, but that window is closing fast. Their security is improving quarterly, and what works today may trigger automatic bans tomorrow.
This game isn’t about finding one perfect method – it’s about constantly adapting as the platform evolves. Stay paranoid, change everything often, and never get tied to any one account or domain.
For those with the technical skills and patience, Snap ads can still print money. Good luck with your card game, and you’ll be swimming in profits.
(c) Telegram: d0ctrine
While TikTok and Facebook have recently started tightening up their fancy AI-powered verification systems, Snapchat is still running with its outdated, non-AI verification processes. It’s like they missed the security memo everyone else got. Their prehistoric verification system is great for carders who have been pushed out of other platforms due to advanced fraud detection.
Snapchat Ads
While the major platforms have tightened up their ad platforms, Snapchat is in that perfect middle ground — popular enough to drive serious traffic, but with security holes you can exploit without breaking a sweat. Their user base is largely made up of teens and young adults with disposable income and zero impulse control. These kids will click on anything shiny that will stop their friends from taking selfies with a dog filter.
What else makes Snap’s ad platform so great is its simplicity. The targeting works well enough to zero in on a specific teen demographic — sneakerheads, aspiring influencers, makeup-obsessed people — allowing you to promote products these kids desperately want. Dropshipping fake streetwear? Questionable supplements? Fake designer crap? Card-sniffing scam pages? Snapchat’s teen market will eat it up. They don’t vet your ads like Facebook’s digital Gestapo, and if you know what you’re doing, their payment system has weaknesses you can exploit all day long.
Antifraud and cloaking
You need to understand that Snapchat’s core security revolves around checking your landing pages. Their scanners scan your landing URLs for fraudulent schemes, malware, or content they’ve previously banned. Once they flag your domain, it’s dead — they blacklist it before you can use your card credits.
Using clean cards isn’t that important, what matters is that you rotate domains. Their main payment processor is dumb as a rock: no anti-fraud, no 3DS, nothing. When your card is declined or Snap bans an account, they don’t just kill your profile — they destroy your entire domain. That URL is gone forever. You need to keep a stack of fresh or old domains ready, all pointing to your main server.

For added protection, set up server-side cloaking, which shows Snap's crawlers a legitimate page while sending real users to your cash-rich site. The crawler uses predictable IP ranges and user-agent strings - filter these out and send them a clean, compliant landing page while real visitors see the shady crap you're actually advertising. This part is a bit of a complex topic, and I covered parts of it in the "Cloaking and carding of advertisements" thread.
Remember: one domain = one account. If any part fails, delete everything and start over. In practice, this means you can set up one server, map multiple domains to it, and continue showing ads with new combinations. This server becomes your base of operations while you cycle through domains and maps, maximizing your efficiency without having to rebuild your entire infrastructure each time.
One of the ways anti-fraud systems detect and reject your transactions is by checking whether the card has been used elsewhere. This means that cards that are resold at multiple stores and frequently re-checked for validity will be rejected outright.
Luckily, BinX has a free tool that will help you assess whether the card you are about to buy is being resold at multiple stores. And the best part is that it’s all FREE:
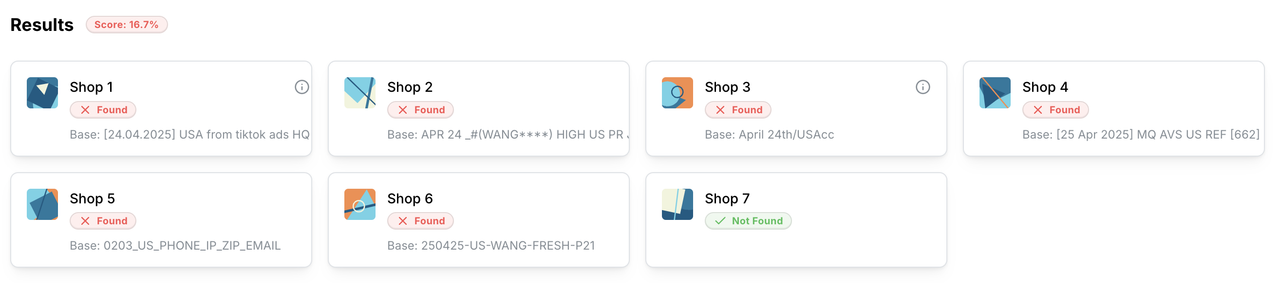
Now you’ll know if a card is bad before you buy it.
Check it out here: https://binx.cc/tools/resell
Prepay Ad Balance
Another great thing about Snapchat advertising is how easy it is to use the prepay option. Prepay Ad Balance is arguably the best tool for carders on any ad platform — it forces Snapchat to let you top up your balance up front, instead of their standard recurring billing.
Why is this important? With standard billing, Snapchat (or other platforms) charge your card certain amounts as ads run. Every charge is another damn roll of the dice — will the card work or has it already been reported? One rejection and your entire operation will collapse. But with prepay, you’ll empty the entire card in one fell swoop before any chargebacks occur. Essentially, you’re preloading all the funds on that card before it’s destroyed.
Load up a new card with $500–$1,000, burn through that balance with aggressive campaigns, and by the time the cardholder notices and reports it, you’ve already converted it into traffic. No more sweating every time Snap’s payment system decides to charge your card.
Unlike Facebook or TikTok, where pre-pay is a standard option, Snapchat hides this feature. It only appears under certain conditions that I haven’t fully mapped out yet. One reliable trigger seems to be using high-income zip codes when initially setting up a business account — try 90210 (Beverly Hills), 76092 (Southlake, TX), or other wealthy areas.
Don’t worry about using fancy zip codes during signup — the business address you enter has absolutely nothing to do with your card’s payment details. You can still add any card with any billing address to your account later. The high-income zip code is only needed for Snapchat’s system to offer the prepaid option.
When the prepaid option appears, add your card and pounce on it. This is your ticket to getting the most out of each card before it burns out.
Requirements and Process
With all that said, here’s the process:
Setting up your account:
- Create a new account using residential proxies (mobile IPs work best)


- Create a business account with a high income zip code (90210, 76092) to enable the prepay option.
- Keep your device's fingerprints squeaky clean - new browser profiles for every operation
- Be sure to take advantage of any promotions they offer, this will not only help you maximize your credits, but will also help you appear legitimate.

- Don't waste time on detailed business profiles - you only need the basic information
Payment method:
- Use only high limit cards
- Match the zip code EXACTLY for billing - this method doesn't even require a correct address, just the zip code.
- ALWAYS pre-pay your balance in one go - drain the card before refunding the payment
- Keep 3-5 spare cards ready in case something goes wrong.
Domain Management:
- Follow the golden rule: one domain = one account
- Keep a set of domains ready - once they are marked they will become nuclear waste
- Set up proper cloaking that will show Snaps scanners a clean site, while real users will see your money pages
Campaign structure:

- Start with modest daily budgets ($50-$100) to avoid manual checks
- Target impulsive teens with disposable income and zero skepticism
- Create ads that align with organic content
- Change everything frequently - domains, card accounts, creative
Remember: if any part of your transaction is flagged, throw it ALL away and start over. Don't get sentimental about accounts or domains - they are disposable tools, not pets. Also, if you overdo it by doing 5,000-10,000 on new accounts, Snap (like FB) may ask for a mini-spend code, although I have not encountered this at all.
Conclusion
Snapchat remains one of the last semi-vulnerable major ad platforms for carding, but that window is closing fast. Their security is improving quarterly, and what works today may trigger automatic bans tomorrow.
This game isn’t about finding one perfect method – it’s about constantly adapting as the platform evolves. Stay paranoid, change everything often, and never get tied to any one account or domain.
For those with the technical skills and patience, Snap ads can still print money. Good luck with your card game, and you’ll be swimming in profits.
Disclaimer: The information provided in this article, as well as all my articles and guides, is for educational purposes only. This is an exploration of how scams work and is not intended to promote, endorse, or facilitate any illegal activity. I cannot be held responsible for any actions taken based on this material or any material posted by my account. Please use this information responsibly and do not engage in any criminal activity.
(c) Telegram: d0ctrine
