Christmas is coming, and what’s better than a shiny new machine under the tree? But let’s be real, we can’t exactly give away a damn machine. So what’s the next best thing for a bunch of nerds like us? A brand new high-end gaming PC, that’s what. And where are we going to get one of these beauties? NZXT BLD, that’s where.
NZXT are the makers of expensive PC cases and coolers that look like they were designed by a horny teenager. Now they’re selling pre-built systems through their “BLD” service. They promise custom gaming rigs, but their security is about as effective as a wet paper bag.
We’re targeting NZXT’s BLD service, where they build custom PCs from high-end components. High-end crap has driven up prices, and their security is a fucking joke. Perfect for us.
Get your cards ready, fire up your proxies, and show NZXT what happens when you put aesthetics ahead of actual security.
Why NZXT BLD?
NZXT BLD has a lot going for it for carders. They have everything a gamer could want, all wrapped up in custom rigs with hefty markups. There are some vulnerabilities in their security that we can exploit.
Here's why the NZXT BLD is worth our time:
NZXT BLD is a high-value target with a loyal customer base and a profit margin that justifies the effort. Their security is flawed, and we're going to exploit every one of them.
Reconnaissance
Let's put on our hacker hoodies and see what we're dealing with. We fired up Chrome Dev Tools and started poking around NZXT's BLD site.
Peeling back the layers of their supposedly custom-built site reveals the ugly truth: it’s just Shopify. And if you’ve been paying attention to our guides, you’ll know that Shopify’s payment processor is nothing more than Stripe. So what are we dealing with here? You guessed it: Stripe Radar.
Don’t get me wrong, there’s no anti-fraud voodoo on the front end. Forget about impersonating a real shopper; that’s a waste of time. No need to wander around like some shopper window shopping like we do on other sites. NZXT doesn’t do any fingerprinting shit, either. Sure, they collect some basic information, but your run-of-the-mill anti-detection browser will have no problem spoofing that shit.
NZXT’s Payment Process and BLD Process
NZXT’s setup runs on Shopify, which means they ride the Stripe payments rails, and that includes running the infamous Stripe Radar for their BLD service. Radar's fraud detection algorithms are a bitch, but NZXT hasn't exactly beefed up their defenses. We've got a little wiggle room.
Before you even think about hitting NZXT, brace yourself. Read our articles: "Carding Bites: Understanding Shopify" and "Why Purchased Cards Never Work, and What You Can Do About It". They'll give you an idea of how to approach this. In short, you need a crystal-clear IP and a fresh, first-hand card that hasn't been touched by some dirty Stripe checker.
Here’s the thing: When you enter your card details, Stripes is already assessing you. They scrutinize your card number, expiration date, CVV, and billing address. They assign your transaction a risk score based on the card’s history, your spending habits, and the reputation of your IP address. If that risk score is too high, you’ll run into a 3D Secure problem. That’s where you need a Non-VBV card, or one that can bypass 3DS. If you’re safe and avoid the 3DS bullet, your payment gets the green light even if you use a VBV card.
NZXT’s system isn’t rocket science, but don’t be sloppy. You still need clean cards, reliable proxies, and a decent anti-detection setup to slip through Stripes’ network.
Requirements:
Process:
Advanced NZXT Flex
NZXT Flex, their desktop subscription, is a sneaky way to bypass Stripes fraud detection. The monthly fees are small enough to go unnoticed. It’s a crap deal for legitimate customers, but who cares?
You’ll need a US phone number for SMS verification. Rent one from a service like smspool.net. The tricky part is ID verification. They use flaw.co, which is tied to Stripes ID verification, and you’ll need a selfie and ID.
Getting approved is easy if you can fake an ID check. If you've dealt with ID checks before, this will be a piece of cake. If not, I'll show you how to combat these scams in the future.
Here's the game: Pick a PC, and since you're only hooked for the first month, load it up with the most expensive components. Subscribe with a card, confirm via SMS, and once the check is approved, the beast is on its way. Think of it as a free trial for a top-notch PC. Cancel before the next payment comes through, or let the cardholder or NZXT handle it. Now none of this has anything to do with you.
Conclusion
So, there you have it, a plan to turn NZXT into your personal tech treasure chest. NZXT BLD and Flex are child’s play if you have half a brain. You now have access to top-end gaming rigs that will make your setup the envy of every miner in the COD lobby.
So get ready. Use clean cards, reliable proxies, and a properly configured anti-detection browser. Follow this guide and read the other guides I’ve written on Shopify and Stripe, and your chances of success will skyrocket. Use this knowledge wisely, and remember how you got here.
(c) Telegram: d0ctrine
NZXT are the makers of expensive PC cases and coolers that look like they were designed by a horny teenager. Now they’re selling pre-built systems through their “BLD” service. They promise custom gaming rigs, but their security is about as effective as a wet paper bag.
We’re targeting NZXT’s BLD service, where they build custom PCs from high-end components. High-end crap has driven up prices, and their security is a fucking joke. Perfect for us.
Get your cards ready, fire up your proxies, and show NZXT what happens when you put aesthetics ahead of actual security.
Why NZXT BLD?
NZXT BLD has a lot going for it for carders. They have everything a gamer could want, all wrapped up in custom rigs with hefty markups. There are some vulnerabilities in their security that we can exploit.
Here's why the NZXT BLD is worth our time:
- High value inventory: $3000+ PCs equipped with the latest hardware. Easy profit (or FPS) for us.
- Brand Recognition: NZXT is a big name in the PC world. Having their logo on a resale listing will attract buyers.
- Terrible security: For a company selling such expensive equipment, fraud prevention measures are inadequate.
NZXT BLD is a high-value target with a loyal customer base and a profit margin that justifies the effort. Their security is flawed, and we're going to exploit every one of them.
Reconnaissance
Let's put on our hacker hoodies and see what we're dealing with. We fired up Chrome Dev Tools and started poking around NZXT's BLD site.
Peeling back the layers of their supposedly custom-built site reveals the ugly truth: it’s just Shopify. And if you’ve been paying attention to our guides, you’ll know that Shopify’s payment processor is nothing more than Stripe. So what are we dealing with here? You guessed it: Stripe Radar.
Don’t get me wrong, there’s no anti-fraud voodoo on the front end. Forget about impersonating a real shopper; that’s a waste of time. No need to wander around like some shopper window shopping like we do on other sites. NZXT doesn’t do any fingerprinting shit, either. Sure, they collect some basic information, but your run-of-the-mill anti-detection browser will have no problem spoofing that shit.
NZXT’s Payment Process and BLD Process
NZXT’s setup runs on Shopify, which means they ride the Stripe payments rails, and that includes running the infamous Stripe Radar for their BLD service. Radar's fraud detection algorithms are a bitch, but NZXT hasn't exactly beefed up their defenses. We've got a little wiggle room.
Before you even think about hitting NZXT, brace yourself. Read our articles: "Carding Bites: Understanding Shopify" and "Why Purchased Cards Never Work, and What You Can Do About It". They'll give you an idea of how to approach this. In short, you need a crystal-clear IP and a fresh, first-hand card that hasn't been touched by some dirty Stripe checker.
Here’s the thing: When you enter your card details, Stripes is already assessing you. They scrutinize your card number, expiration date, CVV, and billing address. They assign your transaction a risk score based on the card’s history, your spending habits, and the reputation of your IP address. If that risk score is too high, you’ll run into a 3D Secure problem. That’s where you need a Non-VBV card, or one that can bypass 3DS. If you’re safe and avoid the 3DS bullet, your payment gets the green light even if you use a VBV card.
NZXT’s system isn’t rocket science, but don’t be sloppy. You still need clean cards, reliable proxies, and a decent anti-detection setup to slip through Stripes’ network.
Requirements:
- Cards: Fresh, unused cards are a must. Don’t waste time looking for “magic” BINs — that’s an amateur’s game. Instead, match the typical BIN credit limit and income level to your billing address’s zip code. For example, use premium card BINs for wealthy areas and standard BINs for middle-class areas. And if you’ve run a card through any Stripe-based checks before it’s burned — throw it away and buy a new one.
- Proxies: Pure residential proxies that match the map location. Data center proxies are a red flag.
- Anti-detect browser: a must to mask your digital fingerprint.
- Drop address: a clean address that hasn't been burned, but it doesn't matter if you set it up correctly.
Process:
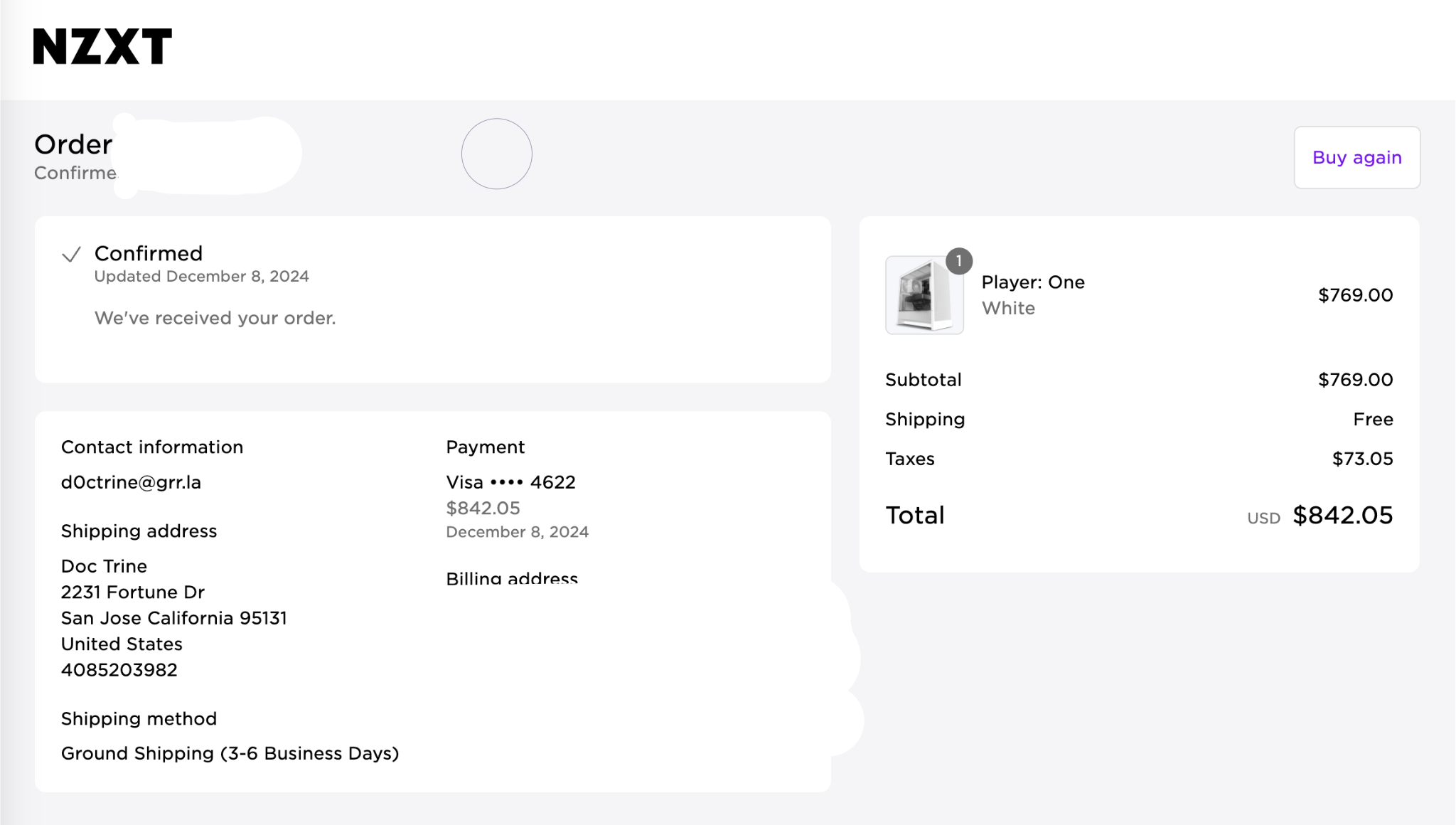
- Launch your antidetect browser and connect to your proxy server.
- Head over to NZXT BLD and pick out your dream PC.
- When placing an order, please enter your card details. Don't copy and paste like some script kiddie.
- If you got a 3DS, you're probably screwed. If not, hold your breath.
- If the payment goes through, you're golden. If not, try another card or move on.
Advanced NZXT Flex
NZXT Flex, their desktop subscription, is a sneaky way to bypass Stripes fraud detection. The monthly fees are small enough to go unnoticed. It’s a crap deal for legitimate customers, but who cares?
You’ll need a US phone number for SMS verification. Rent one from a service like smspool.net. The tricky part is ID verification. They use flaw.co, which is tied to Stripes ID verification, and you’ll need a selfie and ID.
Getting approved is easy if you can fake an ID check. If you've dealt with ID checks before, this will be a piece of cake. If not, I'll show you how to combat these scams in the future.
Here's the game: Pick a PC, and since you're only hooked for the first month, load it up with the most expensive components. Subscribe with a card, confirm via SMS, and once the check is approved, the beast is on its way. Think of it as a free trial for a top-notch PC. Cancel before the next payment comes through, or let the cardholder or NZXT handle it. Now none of this has anything to do with you.
Conclusion
So, there you have it, a plan to turn NZXT into your personal tech treasure chest. NZXT BLD and Flex are child’s play if you have half a brain. You now have access to top-end gaming rigs that will make your setup the envy of every miner in the COD lobby.
So get ready. Use clean cards, reliable proxies, and a properly configured anti-detection browser. Follow this guide and read the other guides I’ve written on Shopify and Stripe, and your chances of success will skyrocket. Use this knowledge wisely, and remember how you got here.
Disclaimer: The information provided in this article, as well as all my articles and guides, is for educational purposes only. This is an exploration of how scams work and is not intended to promote, endorse, or facilitate any illegal activity. I cannot be held responsible for any actions taken based on this material or any material posted by my account. Please use this information responsibly and do not engage in any criminal activity.
(c) Telegram: d0ctrine


